Insights Hub
- All
- Consulting Services
- Cybersecurity Technology
- Managed Services
- Public Safety
- Resources

Brite’s Cybersecurity Ecosystem is Now Bigger and Better with Managed Crowdstrike
At a Glance: While high-profile cyber attacks may grab the headlines, the truth is that attacks can happen to any organization at any time. Often, companies struggle with having the resources and tools necessary to protect their business, as well as lacking visibility across all their endpoints. As a new Crowdstrike MSSP partner, Brite is…

Penetration Testing: What it is and Why Your Organization Needs it
At a Glance: Even with security measures in place, vulnerabilities within an organization’s cybersecurity infrastructure can go undetected. By simulating real-world attacks, penetration testing helps uncover weaknesses before cyber criminals can exploit them. Brite offers comprehensive penetration testing services that help identify and address potential security weaknesses. At Brite, we believe that good enough…

Keep Your Organization Safe and Going Strong with Brite’s Managed Services
At a Glance: Brite offers 24/7 comprehensive managed IT and cybersecurity services through BriteStar and BriteProtect. BriteStar protects and manages IT infrastructure for companies across the country. BriteProtect secures businesses by continuously monitoring, managing, and responding to threats before they escalate any further. In today’s rapidly evolving digital landscape, organizations need robust IT and…
Embracing 5G in Public Safety – On-demand Webinar
Officers, firefighters and paramedics alike need secure, reliable and fast communications. They rely on one router to connect the increasing number of critical devices in their vehicle back to HQ. That’s where Sierra Wireless comes in with three of its newest XR devices using 5G for public safety. This on-demand webinar keeps public safety viewers…

Enhance Your Cybersecurity with Managed Open XDR
At a Glance: Managed Open XDR can help with alert fatigue and limited resources. Brite proudly offers unparalleled protection through our own managed cybersecurity service called BriteProtect, which leverages Open XDR. Our Managed Open XDR services provide many benefits to organizations and help solve common industry problems. It goes without saying that you need cybersecurity…
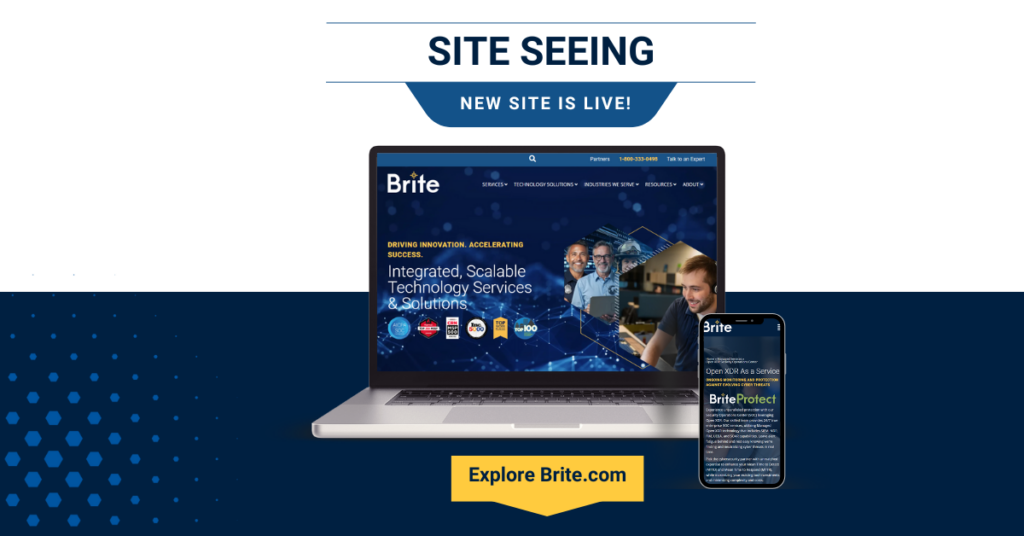
Brite Unveils New Website
At a Glance: Brite is pleased to announce it has launched a new version of its website. Brite.com was redesigned with the user in mind. The new site provides improved navigation and accessibility and greater consistency from a brand perspective. After months of gathering user feedback and conducting extensive research, Brite is pleased to…
Bank on BriteProtect to Keep Your Financial Institution Safe
At a Glance: Financial services firms are way more likely than other companies to be targeted by cyber criminals. Brite has the cybersecurity solution for financial institutions: our Managed Open XDR platform called BriteProtect. This solution integrates your existing security tools and data sources into a single detection and response platform, leading to improved risk…

Brite Celebrates 25 Years of Serving Public Safety
At a Glance: This year, Brite is celebrating 25 years of serving the public safety sector. We look forward to doing so for many years to come! We’ve achieved several key public safety milestones since 1999. We offer a wide range of technology and solutions, including mobile computing, license plate readers, and much more. …

Fixed Price Managed IT Services: How BriteStar Can Help You Budget
No one likes the unexpected. Especially when it comes to surprise costs. Let’s be real. Every business feels every penny, whether it’s a multi-billion-dollar company or the go-to local ice cream shop. As beneficial a product or service is to business operations, there’s always a financial impact. That’s why when it comes to IT and cybersecurity, our managed service offering,…

Phishing Attacks: A Continuously Evolving Threat
Cyber security is a game of cat and mouse. Attackers find endless ways to infiltrate companies of all sizes and industries for monetary gain. At the same time, companies and IT services are implementing tools and procedures to mitigate the risk of phishing attacks. The key for IT and security professionals is to constantly be evaluating evolving…
