Cybersecurity Techology
Secure your organization with industry-leading, innovative solutions that protect against today's advanced cyber threats and ensure compliance
Securing your organization is our mission. Through partnering with best-in-breed technology providers, Brite’s cybersecurity experts and certified product engineers ensure you’re protected today and tomorrow as your needs evolve. Our strategy? Early threat detection, secure access to those who need it when they need it, identify and protect your data, and ensure compliance.


Integrate and Elevate: Customized Cybersecurity Solutions for Your Organization
Analyze | Elevate | Protect
- We review your current cybersecurity infrastructure and create a tailored roadmap to help improve your approach.
- Our wide-ranging cybersecurity tools and solutions will help identify gaps and safeguard your organization against all threat vectors.
- We provide scalable cybersecurity solutions that evolve alongside your organization, complemented by 24/7 support from dedicated US-based professionals.
What Cybersecurity Technology Solutions Does Brite Offer?
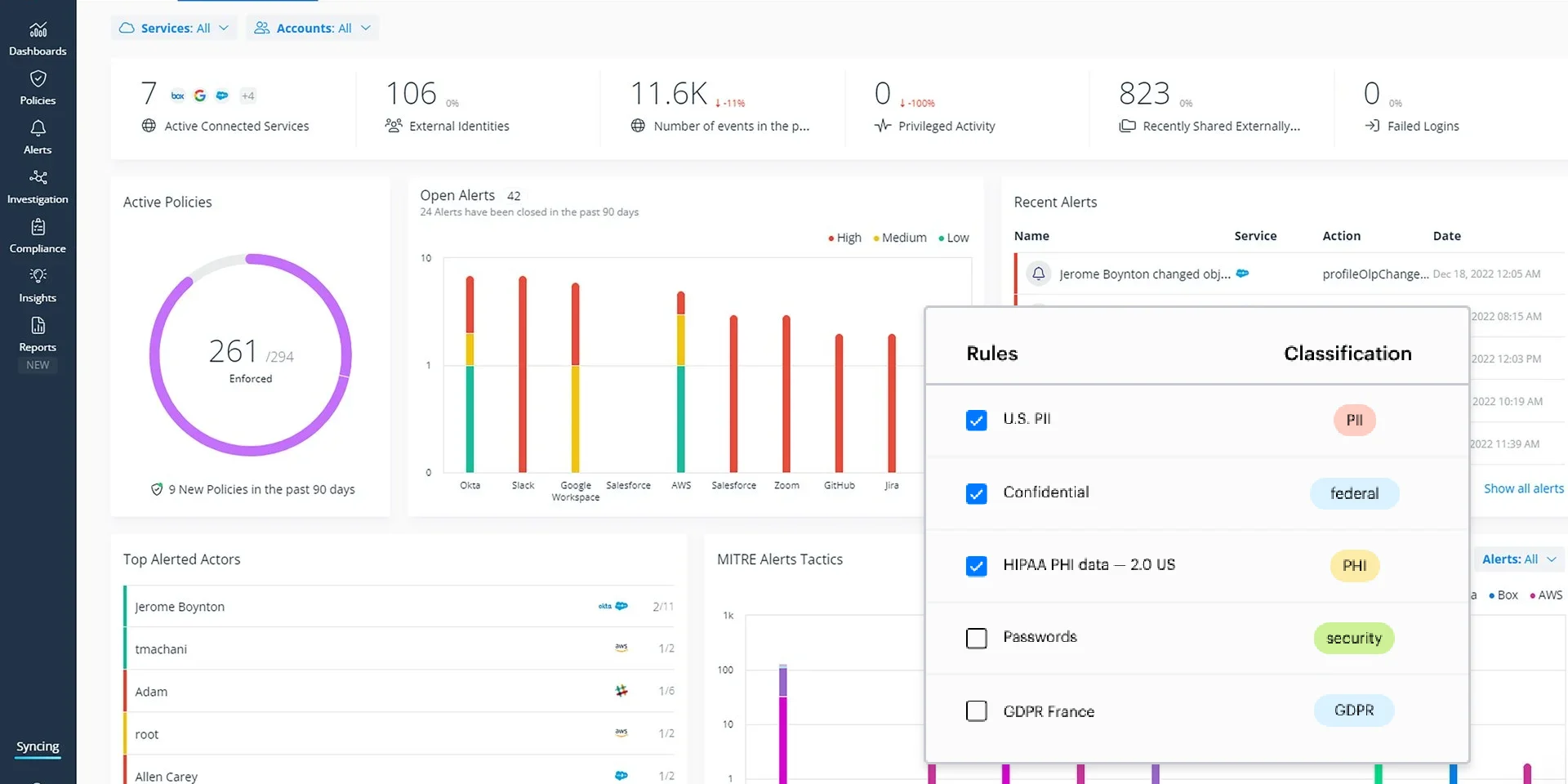
Our suite of tools and rule sets simplify the daunting task of ensuring your data is secure, compliant, and always recoverable. With services like Data Discovery, Data Protection, and Data Loss Prevention, we help you maintain the integrity of your most valuable information.
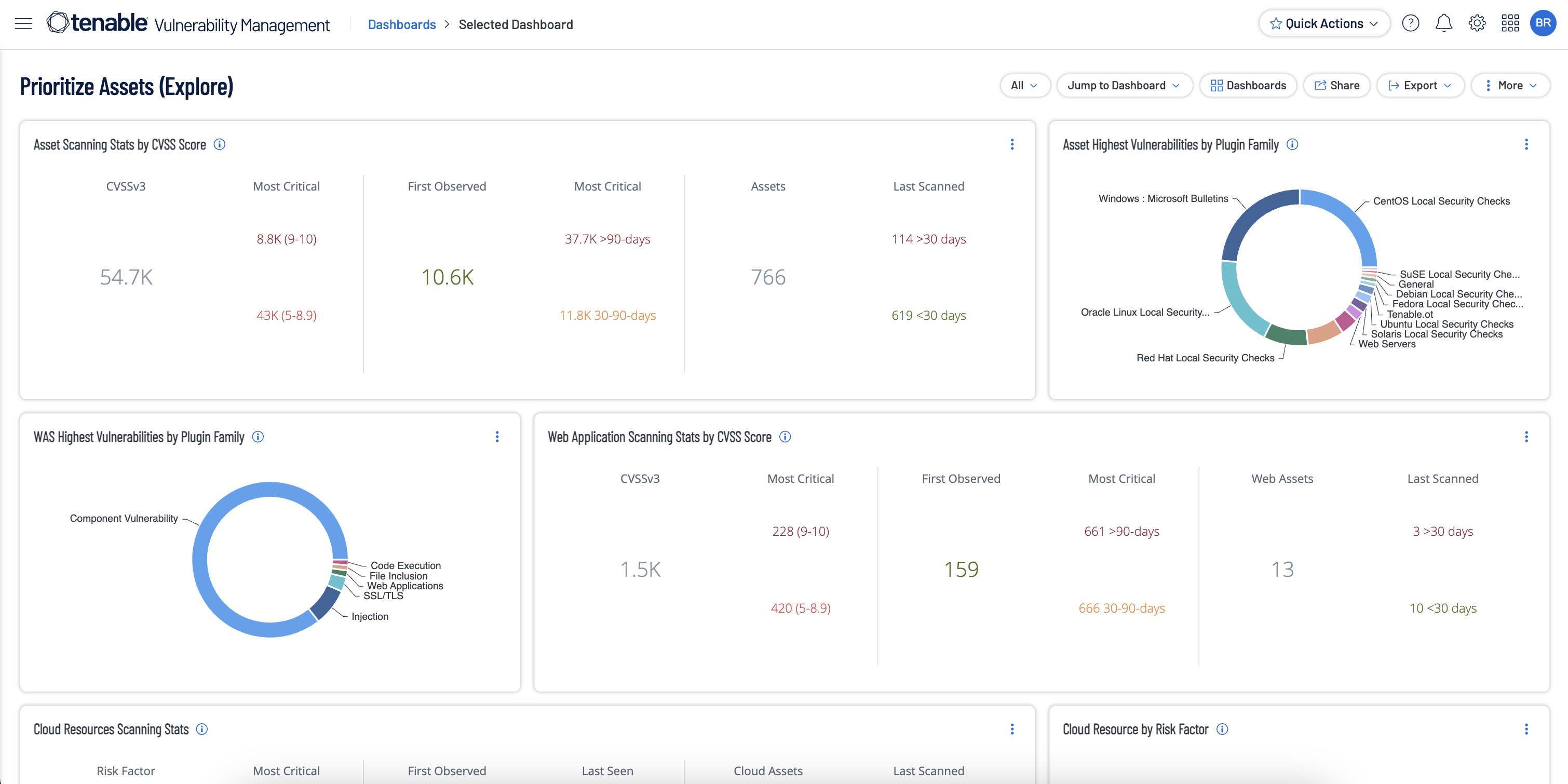
You can't protect what you can't see. Gain unmatched asset insight and visibility with point-in-time discovery or continuous inventory management. Accurately measure your attack surface, identify vulnerabilities, and prioritize the remediation plans.
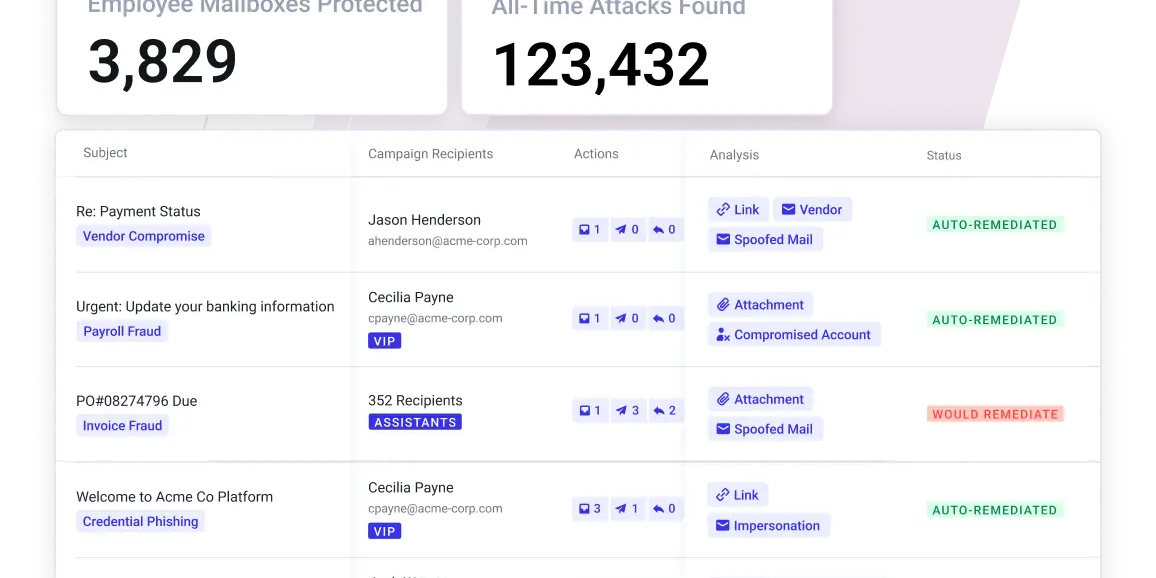
Over 80% of attacks start with email. Protect your organization with our Email Security solutions, offering advanced threat detection, encryption, spam filtering, and phishing protection for complete inbound and outbound safety.
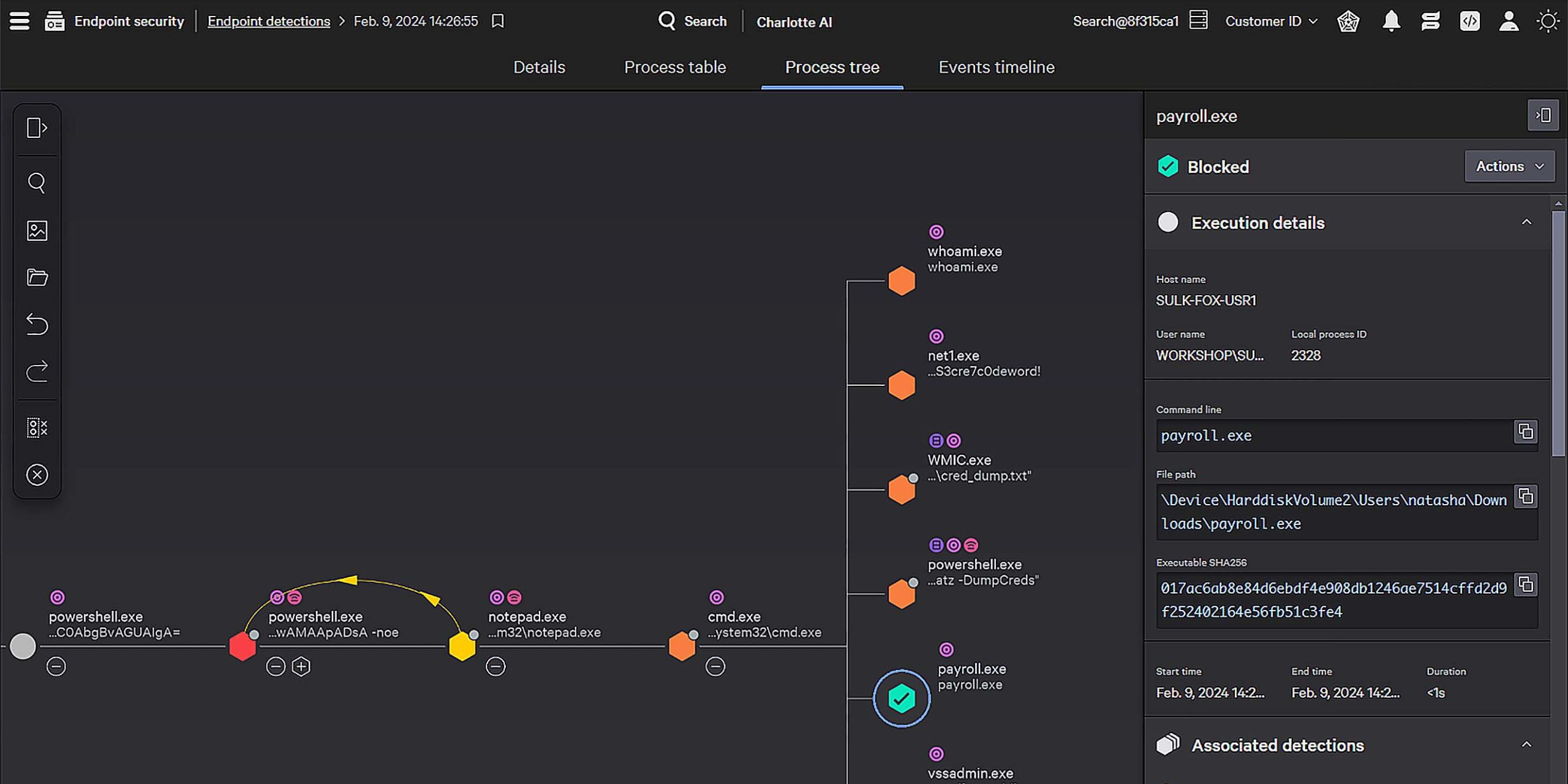
Ransomware continues to be a leading threat to all organizations. We safeguard your data and devices, ensuring comprehensive security regardless of your team’s location. With our industry-leading advanced protection tools, you can maintain peace of mind while empowering your workforce to collaborate safely from anywhere.
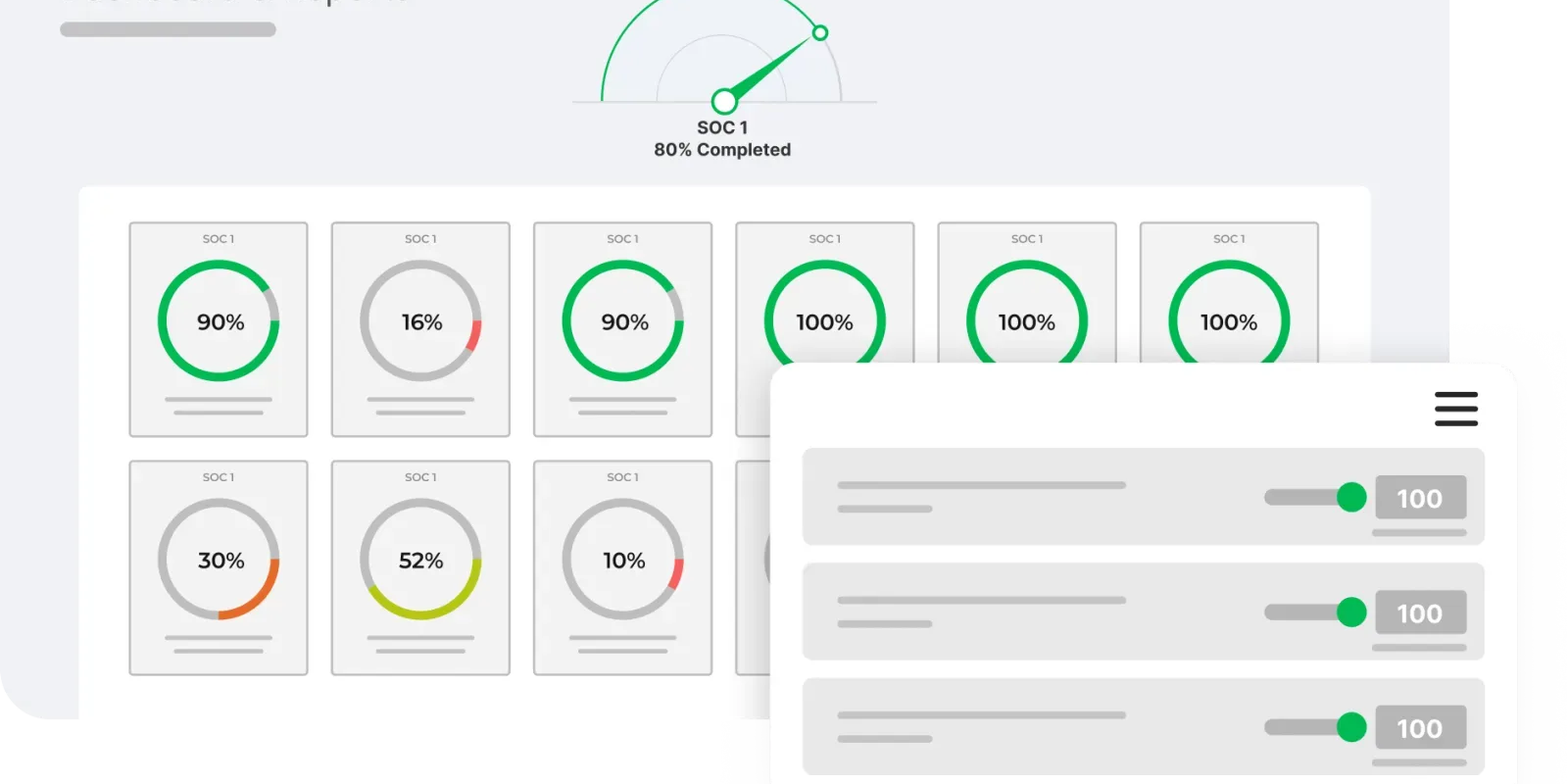
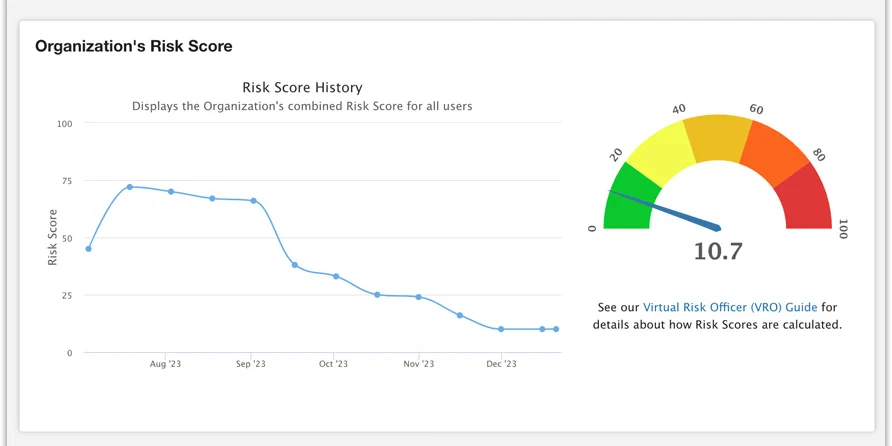
Whether you're working to meet regulatory compliance standards, streamline audits, reduce risks, or establish a best practices roadmap, our Risk and Compliance solutions can help. We focus on reducing costs, improving your security posture, and supporting long-term growth, ensuring you not only comply with regulations but also build a resilient framework for the future.
Identity management is a journey, not just a technology. Brite supports your journey with our Identity Access Management (IAM), Privileged Account Management (PAM), and Identity Governance Administration (IGA) consulting programs. We offer solutions to streamline authentication, ensuring only authorized users access critical information.

Real-time threat prevention and advanced security across the perimeter. To help keep your data safe, Brite perimeter security secures and streamlines your network operations with advanced protection systems that monitor the traffic and watch for unusual patterns tackling threats before they can do harm.
Empower your organization with adaptive cybersecurity education and behavior-driven processes. Brite’s commitment to education and training helps you build a security-conscious culture within your organization to help reduce this risk.
Our SOC solutions safeguard your organization by monitoring, managing, and responding to threats before they escalate into incidents. Whether you choose to integrate our services or let our experts handle it all, you can trust Brite to keep your organization secure and operations running smoothly, 24/7.
By the Numbers
Featured Resources

Guarding Governments: How Brite Shields Municipalities from Cyber Threats
At a Glance: Municipalities are targeted by a variety of cyber threats every day, from data breaches to phishing schemes – putting sensitive data and public trust at risk. Brite offers a custom, comprehensive cybersecurity defense to keep local governments of all sizes safe from attacks. Brite also provides pro services to support municipalities’ IT…
Video Overview: Eliminate Cyber Risk with BriteProtect
Keeping up with evolving cyber threats while managing complex security tools can be a real struggle. At Brite, we’ve developed a comprehensive solution to this problem in the form of our managed cybersecurity service called BriteProtect. This provides 24/7 expert-managed services that integrate seamlessly with your existing investments, thereby reducing complexity and costs. With our…

Video Overview: Brite People. Brite Solutions.
Here at Brite, people and technology are at the core of everything we do, and we specialize in IT, cybersecurity, and public safety technology. Our company has come a long way since it was originally founded in 1983 as a custom computer manufacturer in Rochester, NY. Today, Brite is dedicated to keeping communities and organizations…
Let Brite Fortify Your Email Security with Abnormal’s AI-Centered Approach
At a Glance: Email is one of the most vulnerable points in an organization’s cybersecurity strategy. Phishing attacks, spear-phishing, and other social engineering tactics have become more sophisticated, making traditional email security measures less effective. Enter Abnormal Security, an innovative cybersecurity company that is transforming how organizations defend against email-based threats. Brite’s partnership with Abnormal…

The Power of Cybersecurity Consolidation: Why SMBs Need a Unified Approach
At a Glance: Many small-to-medium businesses (SMBs) face a growing barrage of cyber threats and struggle to keep pace with sophisticated attackers. While large organizations have dedicated IT teams and substantial budgets that can afford to integrate best-in-breed solutions, SMBs don’t have that luxury. The solution for SMBs? Consolidation. At Brite, we employ an Open…
Unveiling the annual Brite SOC Analyst Report: Key Insights and Trends in Cybersecurity
Introducing the annual Brite SOC Analyst Report – your resource for insights from experts with a finger on the pulse of the cybersecurity industry. As a managed security service provider (MSSP), it is crucial that we understand the various types of threats our customers are facing and that we stay ahead of the evolving threat…

Introducing Sevco Security: The Missing Link in Asset Intelligence
At a Glance: New Partner Announcement: Brite is excited to introduce Sevco Security as our latest cybersecurity solutions partner. What Sevco Does: Provides continuous asset intelligence, real-time vulnerability identification, and security gap analysis. Who It’s For: Enterprises in Financial Services, Insurance, Manufacturing, Healthcare, Tech, and beyond looking to eliminate security blind spots and strengthen cyber…

Brite’s Cybersecurity Ecosystem is Now Bigger and Better with Managed Crowdstrike
At a Glance: While high-profile cyber attacks may grab the headlines, the truth is that attacks can happen to any organization at any time. Often, companies struggle with having the resources and tools necessary to protect their business, as well as lacking visibility across all their endpoints. As a new Crowdstrike MSSP partner, Brite is…

Enhance Your Cybersecurity with Managed Open XDR
At a Glance: Managed Open XDR can help with alert fatigue and limited resources. Brite proudly offers unparalleled protection through our own managed cybersecurity service called BriteProtect, which leverages Open XDR. Our Managed Open XDR services provide many benefits to organizations and help solve common industry problems. It goes without saying that you need cybersecurity…
Brite Unveils New Website
At a Glance: Brite is pleased to announce it has launched a new version of its website. Brite.com was redesigned with the user in mind. The new site provides improved navigation and accessibility and greater consistency from a brand perspective. After months of gathering user feedback and conducting extensive research, Brite is pleased to…
